Login Access and Scraping Access Should Not Reuse One Proxy Setup
Login access and scraping access should not automatically share one proxy setup on a protected site. If login works but scraping starts challenging or slowing down right after, do not assume the pool is simply too weak. In many cases the bigger mistake is reusing one route for two very different jobs: identity-sensitive login traffic and higher-frequency collection traffic. The first step is to separate continuity needs from throughput needs before you replace browsers, proxies, and headers all at once.
Login access usually needs a steadier identity. Scraping access often needs stricter request pacing, rotation rules, and failure isolation. When both run through the same exit pattern, one stage can poison the other. A login flow may create a session under one IP and browser state, then the collection layer rotates too early or changes behavior too sharply. The result looks like random Cloudflare instability even though the real problem is workflow mixing.
Why one proxy setup breaks when login and scraping share it
Protected sites do not judge only whether a request arrives from a usable IP. They also watch whether the next step still looks like the same browser, the same session, and the same user journey. Header consistency matters here too. If your login step wants sticky continuity but your scraping step starts rotating aggressively, the challenge system can treat that handoff as a broken session instead of a normal page transition.
This is why many teams see a clean first pass and then blame the next failure on proxy quality. A better first check is whether the access path changed right after authentication. If you are already seeing challenge drift across requests, start with why a pass can succeed once and then fail on the next step before buying more IPs.
What login traffic usually needs that scraping traffic does not
Login traffic is usually more sensitive to identity continuity than to raw pool size. It benefits from a stable exit, consistent browser state, and fewer abrupt header or transport changes between the challenge page, credential submit step, and the first authenticated page.
That does not mean login always needs the most expensive proxy tier. It means login should avoid unnecessary churn. If your browser state is already fragile, adding fast rotation during authentication can create the exact pattern that protected pages treat as suspicious. For a wider diagnosis path, this article also fits into a broader verification workflow overview when you need to separate session continuity issues from simple IP problems.
What scraping traffic usually needs that login traffic does not
Once authentication is stable, the collection phase often has a different pressure profile. It may need request-rate control, segmented concurrency, route-level retries, and rotation policies that protect the session instead of destroying it. Header consistency can still matter here because some protected routes apply user agent rules on Cloudflare or comparable filtering logic before they decide whether a request looks normal. Scraping traffic can also tolerate different resource mixes depending on whether you are pulling public pages, paginated account data, or lightweight checks after the main session is established.
The key is not to rotate blindly. It is to rotate at the right layer and at the right moment. When operators mix login preservation with pull-phase scale on one shared setup, they often read the symptoms backward: they keep adjusting browsers when the pool policy is wrong, or they keep changing IPs when the browser state is what broke first. If you still are unsure which layer is failing, run a browser-versus-proxy diagnosis before you rebuild the whole stack.
How to split the two stages without overcomplicating the stack
Start by treating authentication as its own continuity zone. Keep the browser state, exit policy, and request shape steady until the protected flow is complete and the first authenticated page loads normally. Only then decide whether the downstream scraping work should stay sticky, rotate in segments, or move to a separate collection path.
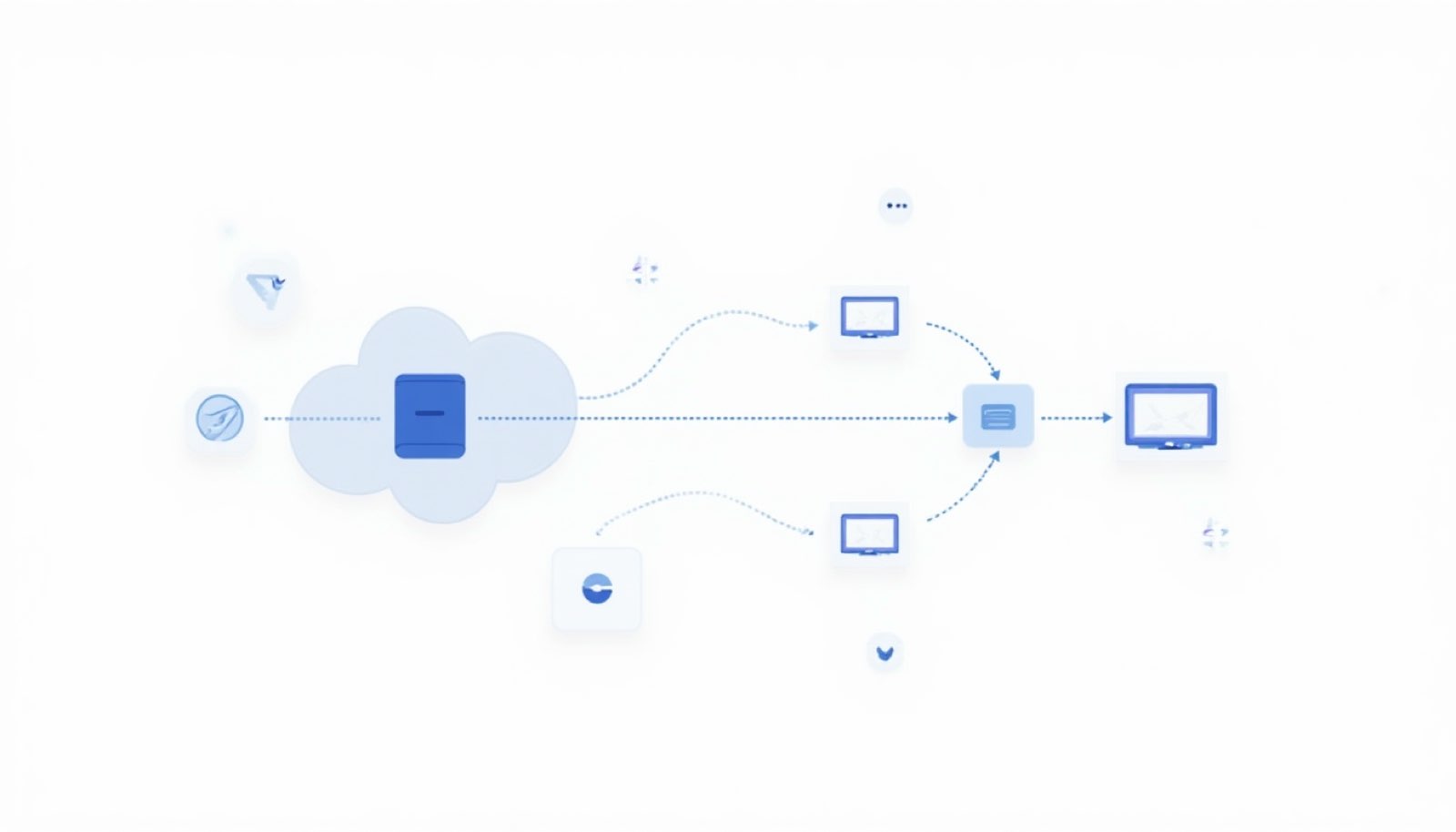
A practical split often looks like this:
- Login and challenge completion use one continuity-preserving route.
- Authenticated browsing checks whether cookies, headers, and page transitions still hold under the same identity.
- Scraping requests use a separate policy based on request density, pagination depth, and retry tolerance.
- Error handling logs which stage broke first instead of lumping all failures into a generic proxy problem.
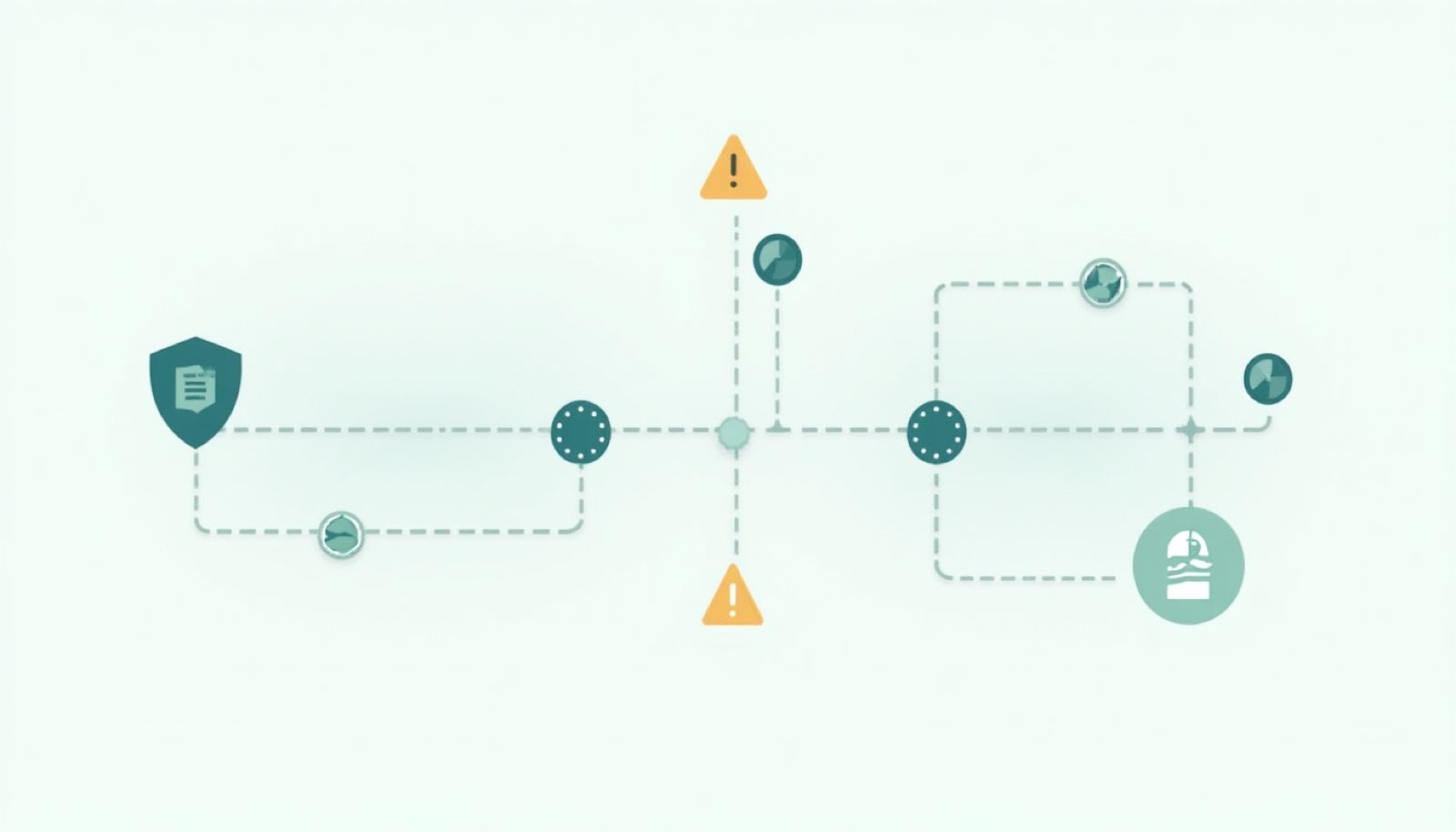
Signals that tell you the setup is mixed in the wrong way
You usually do not need a full rebuild to recognize this pattern. Look for failures such as login succeeding but the first account page re-triggering a challenge, authenticated pages loading only in one browser profile, or scraping becoming unstable only after you added rotation to the same route that handles verification.
Another common sign is that one browser profile keeps passing while another fails with the same proxy pool. That points to state or environment drift much more often than pure IP quality. In that case, compare your symptoms with what to check when Cloudflare verification fails only in one browser before you decide the pool itself is unusable.
When it is actually worth changing the proxy layer
You should change the proxy layer after you have separated task roles and still see the same stage fail for the same reason. If login continuity is preserved, headers are stable, and browser state survives, but the target still rejects the route under realistic pacing, then the current proxy type or quality may indeed be the limiting factor.
Until that point, buying a larger or more expensive pool often hides the real diagnosis. Protected access gets more stable when login identity, session continuity, and scraping policy stop fighting each other. That is also where an API-driven approach becomes easier to control than a pile of ad hoc browser and proxy tweaks.
Final takeaway
Login access and scraping access should not automatically share one proxy setup because they solve different problems. Login is usually continuity-first. Scraping is usually policy-first. If you split those roles early, you can tell whether the real blocker is state loss, browser drift, or resource fit instead of treating every failure as a generic IP shortage.
